Chapter 1
IP Address
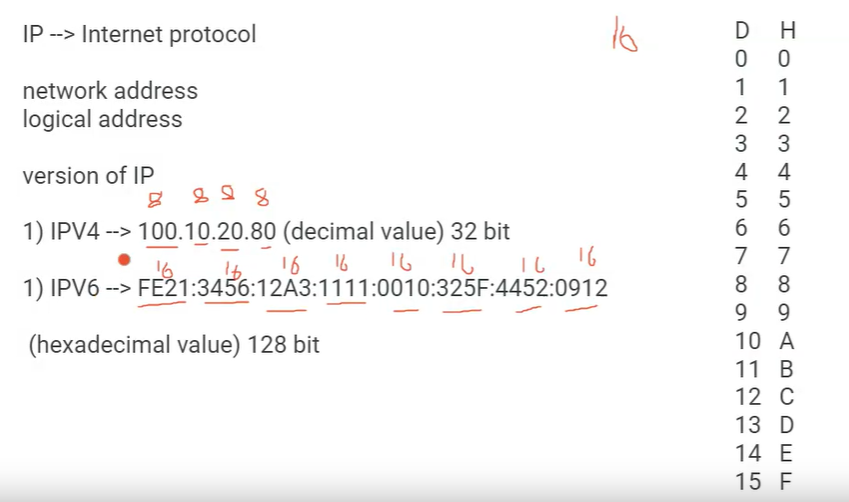
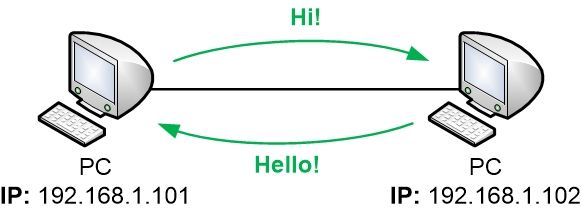
An IP address (Internet Protocol address) is a numerical label assigned to each device connected to a computer network that uses the Internet Protocol for communication. In the context of IPv4 (Internet Protocol version 4),.
which is the fourth version of the Internet Protocol, IP
addresses are 32-bit binary numbers but are commonly expressed in
human-readable form as a series of four decimal numbers separated by periods.
Each decimal number, known as an octet, represents 8 bits of the 32-bit IP
address.
For example, an IPv4 address might look like this:
192.168.1.1. In this address:
– “192” is the first octet.
– “168” is the second octet.
– “1” is the third octet.
– “1” is the fourth octet.
To facilitate human readability, each octet is usually
expressed in decimal form, ranging from 0 to 255. The maximum value for an
octet (8 bits) is 11111111 in binary, which is equivalent to 255 in decimal.
IPv4 addresses are used to uniquely identify and locate
devices on a network. Devices such as computers, servers, routers, and other
networked equipment are assigned unique IPv4 addresses to enable communication
within the network and across the Internet.
However, the growth of the Internet and the increasing
number of connected devices led to the exhaustion of available IPv4 addresses.
To address this issue, IPv6 (Internet Protocol version 6) was introduced, which
uses 128-bit addresses, providing a vastly larger pool of unique addresses
compared to IPv4. While IPv6 adoption is increasing, IPv4 is still widely used,
and transition mechanisms exist to facilitate coexistence between the two
protocols.
Subnetting in IPv4 (Internet Protocol version 4) is a
technique used to divide a larger IP network into smaller, more manageable
sub-networks or subnets. This process helps optimize network performance,
enhance security, and efficiently allocate IP addresses.
IPv4 addresses are 32-bit numerical labels written in the
form of four octets, each represented by a decimal number between 0 and 255.
For example, an IPv4 address might look like this: 192.168.1.1.
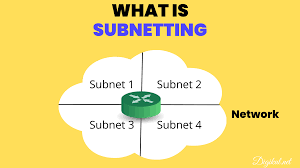
Subneting
Subnetting involves borrowing bits from the host portion of
an IP address to create a dedicated subnet field. This allows network
administrators to create multiple smaller networks within a larger network.
Subnetting provides several benefits:
1. Efficient IP
Address Allocation:
Subnetting allows for more efficient use of IP addresses by
breaking a large address space into smaller, more manageable chunks. This is
especially important as the available pool of IPv4 addresses is limited.
2.Improved Network
Performance:
Smaller subnets can
reduce broadcast traffic and optimize network performance by isolating and
containing local traffic within each subnet.
3. Enhanced Security:
Subnetting can be
used to segment a network, which helps improve security. By isolating different
segments, it becomes more difficult for unauthorized users or malicious
software to traverse the entire network.
4. Flexibility in
Network Design:
Subnetting provides
flexibility in designing and organizing a network. It allows for logical
grouping of devices based on their functions, departments, or locations.
When subnetting, network administrators typically use a
subnet mask to determine the network and host portions of an IP address. The
subnet mask is a 32-bit value, like an IP address, and is written in the same
dotted-decimal format. It consists of consecutive ‘1’ bits representing the
network portion and ‘0’ bits representing the host portion.
For example, consider the IP address 192.168.1.1 with a
subnet mask of 255.255.255.0. In binary, the subnet mask would be
11111111.11111111.11111111.00000000. Here, the first 24 bits are dedicated to
the network (192.168.1), and the last 8 bits are available for host addresses
within that network.
In summary, subnetting is a fundamental networking concept
that provides organization, efficiency, and security in the allocation of IPv4
addresses within a network.
Subneting
Multiple Choice Question
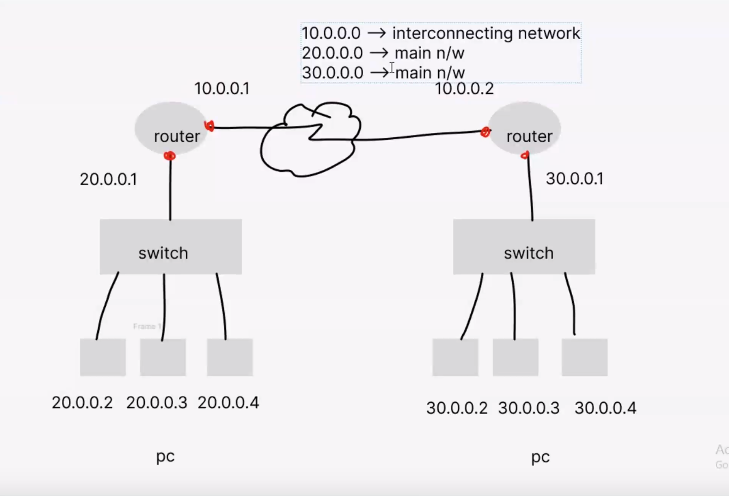
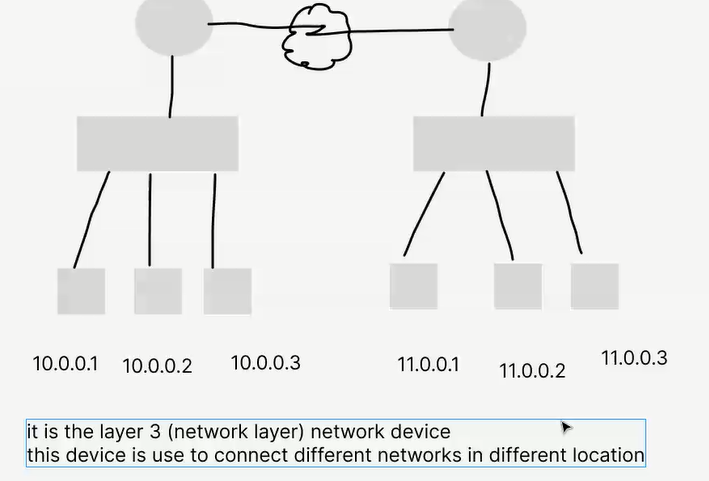
Router
A router is a networking device that forwards data packets between computer networks. It operates at the network layer of the OSI model and uses routing tables to determine the best path for data transmission
Routing Information Protocol
IGRP
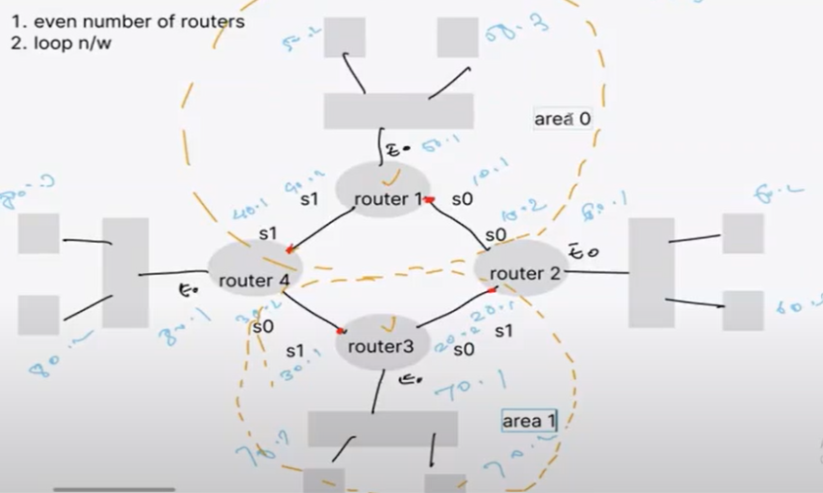
OSPF
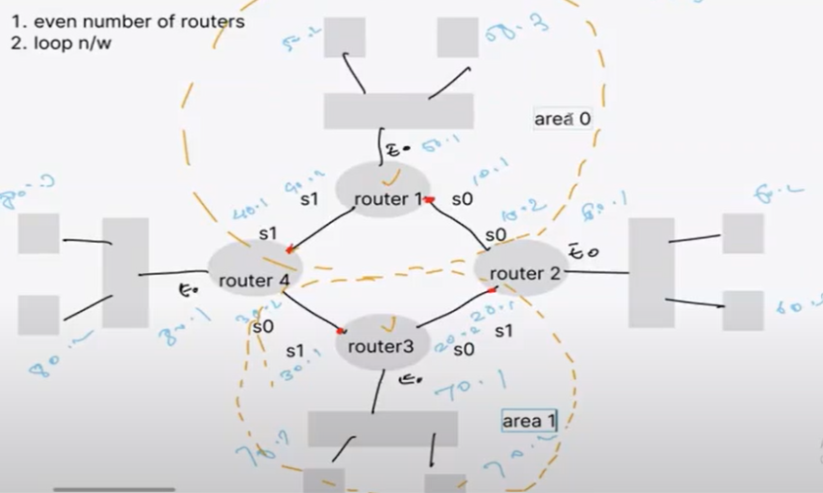
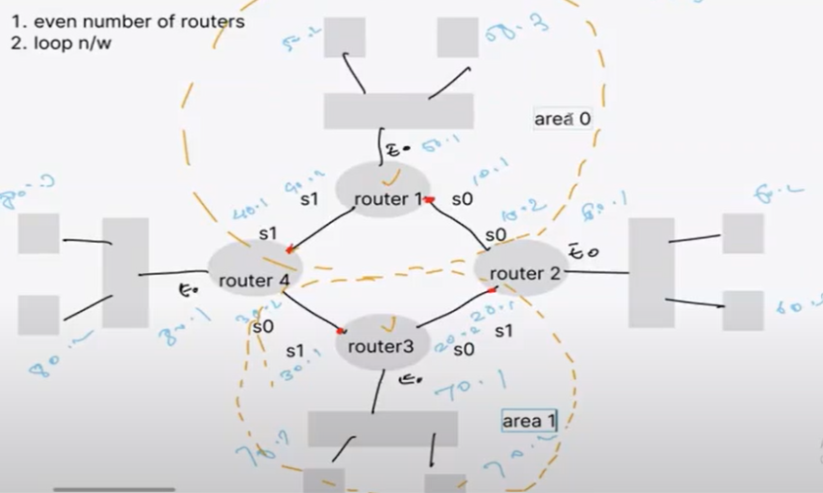
OSPF stands for Open Shortest Path First, and it is a dynamic routing protocol used in computer networks. OSPF is commonly used in large enterprise networks and the internet to help routers exchange routing information and make decisions about the best paths for data to travel.

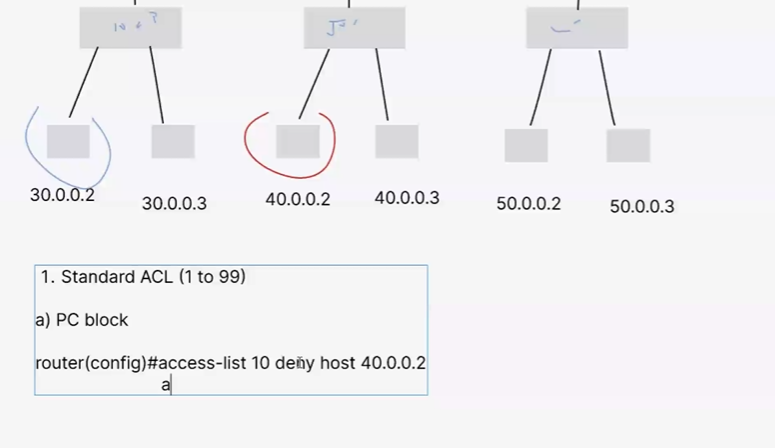
ACL
An access control list (ACL) is a set of rules that defines which users or systems are allowed or prohibited from accessing a specific object or resource within a system. ACLs are also deployed in routers or switches, functioning as filters to regulate and control the network traffic that is permitted to access the network.

SWITCH
n networking, a switch is a device that connects devices together within a local area network (LAN). It operates at the data link layer of the OSI model and is responsible for forwarding data packets between devices based on their MAC addresses. Switches are commonly used in Ethernet networks to improve network performance by reducing collisions and providing dedicated bandwidth to each connected device. They’re more efficient than hubs because they create separate collision domains for each port, thus enhancing overall network speed and efficiency.

OSI MODEL
The OSI (Open Systems Interconnection) model is a conceptual framework used to understand and standardize the functions of a telecommunications or computing system. It divides network communication into seven distinct layers, each responsible for specific tasks and interactions. Here’s a brief overview of each layer: